Superhuman is Spying on You
Over the past 25 years, email has weaved itself into the daily fabric of life. Our inboxes contain everything from very personal letters, to work correspondence, to unsolicited inbound sales pitches. In many ways, they are an extension of our homes: private places where we are free to deal with what life throws at us in whatever way we see fit. Have an inbox zero policy? That’s up to you. Let your inbox build into the thousands and only deal with what you can stay on top of? That’s your business too.
It is disappointing then that one of the most hyped new email clients, Superhuman, has decided to embed hidden tracking pixels inside of the emails its customers send out. Superhuman calls this feature “Read Receipts” and turns it on by default for its customers, without the consent of its recipients. You’ve heard the term “Read Receipts” before, so you have most likely been conditioned to believe it’s a simple “Read/Unread” status that people can opt out of. With Superhuman, it is not. If I send you an email using Superhuman (no matter what email client you use), and you open it 9 times, this is what I see:
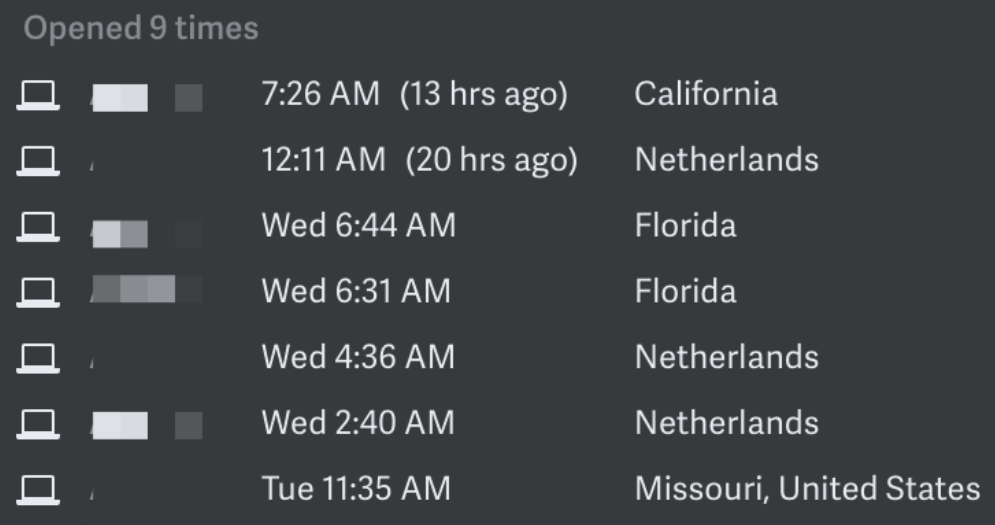
That’s right. A running log of every single time you have opened my email, including your location when you opened it. Before we continue, ask yourself if you expect this information to be collected on you and relayed back to your parent, your child, your spouse, your co-worker, a salesperson, an ex, a random stranger, or a stalker every time you read an email. Although some one-to-many email blasting software has used similar technologies to track open rates, the answer is no; most people don’t expect this. People reasonably expect that when — and especially where — they read their email is their own business.
When I initially tweeted about this last week, the tweet was faved by a wide variety of people, including current and former employees and CEOs of companies ranging from Facebook, to Apple, to Twitter:
It was also met critically by several Superhuman users, as well as some Superhuman investors (who never disclosed that they were investors, even in past, private conversations with me). I want to talk about this issue because I think it’s instructive to how we build products and companies with a sense of ethics and responsibility. I think what Superhuman is doing here demonstrates a lack of regard for both.
First, a few caveats:
- I was invited into the Superhuman service several months ago. I began their onboarding process, was excited to try using it as my primary email client, and bailed out the moment I found out about this spyware functionality.
- Nothing in this post evaluates other things about the Superhuman service. I’m not here to tell you it isn’t fast, isn’t good looking, or doesn’t save you time. I suspect it is all of those things, in fact. So if your response to this post is “BUT I LIKE IT!”, I believe you that there are things to like about it. That is not the subject of this post.
- I know people whom I consider to be ethical people who use workplace software that embeds tracking pixels in emails.
Second, I want to talk about why this particular issue is so important. Not why privacy is important; we are all already learning that the hard way. Rather, why making ethical decisions at the earliest stages of your company is important.
When a company first forms, there are no norms or principles guiding how its people should make decisions. It’s basically just what’s in the founders’ heads. With each decision a company makes, its “decision genome” is established and subsequently hardened. You’ve decided in your first month that you’re only going to hire engineers from Top 10 engineering schools? That’s now part of your genome and will determine the composition of your company. You’ve decided to forgo extra profits by keeping your prices low for consumers? That’s now part of your genome. You’ve decided to employ a single dark pattern to trick users into adding more things to their shopping cart? Part of your genome.
The reason this matters is that what may seem like small decisions early on become the basis for many more decisions down the road. These decisions affect your ethical trajectory as a company. Let’s use the dark pattern example. Maybe the shopping cart thing was pretty minor and you were able to rationalize it internally in a variety of ways, including the fact that the extra item in the user’s cart was inexpensive and provided value (like a product warranty, for instance). Down the road, when employees want to employ more dark patterns, here is how the conversation would go:
Greg: “Hey, we aren’t getting enough people to opt-into our mailing list when they sign up. Can we try maybe unchecking that box by default but using language such that leaving it unchecked opts people in?”
Desi: “Wouldn’t we be intentionally deceiving users if we did that?”
Greg: “Uhhhh, we already add things to your shopping cart that you don’t even ask for!”
Desi: “True. This seems like less of a big deal than that. I guess I’m OK with it.”
If you’ve never worked at a tech company before, this is how things go. When faced with making a product decision that is even mildly uncomfortable, employees often first look towards expressed company principles like “Always put the customer first”, but the next thing they look for is precedent. What other decisions have we made that look like this one? Designers do this. Engineers do this. Product managers do this. Executives do this. It’s an easy way to inform your current decision, and it’s also an easy way to cover your ass. Imagine the above decision was made by a product manager, and later on the company was called out publicly on it. The CEO or Head of Product marches over to the product manager and says “what were you thinking here?!?” The product manager needs only to point to the shopping cart behavior in order to let him or herself off the hook.
The point here is that companies decide early on what sort of companies they will end up being. The company they may want to be is often written in things like “core values” that are displayed in lunch rooms and employee handbooks, but the company they will be is a product of the actual decisions they make — especially the tough decisions.
So back to Superhuman. Here we have a company that professes to create a better email experience mainly through better design and engineering. So far so good! Those who know me know that I would be among the first people to sign up for something like this and also among the most vocal to evangelize it. Heck, I love a certain showerhead so much that I:
- Have bought one for every shower in every place I’ve lived for the past several years.
- Bought one for every member of my leadership team at Twitter for Christmas.
- Used to keep a brand new spare one in my trunk to give away to friends every time the subject came up.
- Turned the damn showerhead emoji on Twitter into a Flipside. Actually, my team did this, but as an homage to my love for it.
In other words, when I see great design, I proactively try to spread it as far and wide as possible.
What I see in Superhuman though is a company that has mistaken taking advantage of people for good design. They’ve identified a feature that provides value to some of their customers (i.e. seeing if someone has opened your email yet) and they’ve trampled the privacy of every single person they send email to in order to achieve that. Superhuman never asks the person on the other end if they are OK with sending a read receipt (complete with timestamp and geolocation). Superhuman never offers a way to opt out. Just as troublingly, Superhuman teaches its user to surveil by default. I imagine many users sign up for this, see the feature, and say to themselves “Cool! Read receipts! I guess that’s one of the things my $30 a month buys me.”
When products are introduced into the market with behaviors like this, customers are trained to think they are not just legal but also ethical. They don’t always take the next step and ask themselves “wait, should I be doing this?” It’s kind of like if you walked by someone’s window at night and saw them naked. You could do one of two things: a) look away and get out of there, realizing you saw something that person wouldn’t want you to see, or b) keep staring, because if they really didn’t want anyone to see them, they should have closed their blinds. It’s two ways of looking at the world, and Superhuman is not just allowing for option B but actively causing it to happen. It’s almost as if Superhuman is aiming a motion-sensitive camera outside people’s windows and sending alerts when there is motion. It’s automated and designed to capture info when your family, your friend, your co-worker, or your victim is not aware. You may think “victim” is too harsh of a word to use here, but remember, we aren’t talking about you. We are talking about anyone who might use Superhuman.
Even though most of the feedback I’ve gotten about raising this issue has been supportive, here is a collection of replies I’ve gotten on Twitter, so we can address them all in one place:
- “Email clients have done this for years. Even Apple does this with iMessage.” — Multiple People. This argument is naive at best and disingenuous at worst. Superhuman’s competitors are Apple Mail, Gmail, and Outlook. Exactly zero of those companies insert a tracking pixel into their emails. Furthermore, both Outlook and iMessage use Read Receipts that are turned off by default and controlled completely by the receiving user. In other words, when you buy a new iPhone or start using Outlook, no one requesting an Outlook or iMessage read receipt can receive one without your explicit permission. Furthermore, even if you do turn those on, it’s a simple one-time receipt… not a log of times and geolocations every time the recipient views the message. Both Microsoft and Apple — as well as other messaging platforms like Twitter, LinkedIn, and Signal — have designed their read receipts in an ethical way. Superhuman has not. Also ask yourself what the backlash would be if a company somehow retrofit these spying capabilities on top of iMessage. What if every single time you viewed someone’s text message, your phone sent a timestamp and location to back to the sender, creating a map of your movements? There’s a reason Apple doesn’t allow this.
- “Other tools like MailChimp, PersistIQ, SendGrid, and MailTrack do this.” — Multiple People. Superhuman is an e-mail client, much like Gmail, Outlook, and Apple Mail. It is not mail automation software. Mass mailing companies, for the most part, use that technology to track open rates and also to *stop* sending out emails to people who haven’t opened them in months. There are indeed some sales-enablement companies that use this technology to track individual opens, and I find that just as creepy. The main point here is: just because technology is being used unethically by others does not mean you should use it unethically yourself. Harmful pesticides have also been around for years. That doesn’t mean you should use them yourself.
-
Where to start with this one from Gary Sheynkman. You, the sender, do not get to decide how I, the receiver, respond to you. Not returning your email right away is not passive-aggressive. It’s often just being busy or prioritizing. As pointed out by Erica, being “left on read” can send unintended hurtful messages. Furthermore, in the workplace, this can be used as a tool to monitor or coerce around-the-clock work.
-
This is from Nick Abouzeid, a Superhuman investor (who did not disclose that, but I got it by going to his website) from the aptly named “Shrug Capital”. This comment gets to the crux of the ethics question we are talking about here. When you are making software, you can either say “lets exploit everything in the world that can act to our benefit” or you can say “lets build something that’s great for the world”. This person looks at all people who use email as potential people to exploit. How many people use email? 2 billion or so? How many of those have images turned off? Probably a tiny percentage. And how many are expecting that every time they open an email from a friend, their friend gets notified with their geolocation? I would guess almost zero. So what this person is essentially saying is that since most people leave their curtains open at night, it’s ethical for the company he funds to film what goes on inside. Furthermore, Superhuman doesn’t even let its own customers turn images off. So merely by using Superhuman, you are vulnerable to the exact same spying that Superhuman enables you to do to others. He is right about one thing though: because of spyware-foisting companies like Superhuman, you should unfortunately turn off all image loading in your email client.
When you start to think about all of the ways Superhuman can be used to violate privacy, you really wonder why The New York Times spent 1,200 words on a tongue-bath that doesn’t even talk meaningfully about privacy issues at all. We don’t need journalism to tell us where venture capitalists are putting other people’s money. We need it to examine the ramifications of the technology we are pushing into the world and in what ways it might shift the Overton Window for Ethics in either helpful or hurtful ways.
There are some bad people out there, so what are some bad things that people can do with technology like this? Here are just a few:
- An ex-boyfriend is a Superhuman user who pens a desperate email. Subject: “I’ve been thinking about us”. He sends it to his former partner. She reads it when she gets to work in Downtown Los Angeles at 9am. She reads it again before dinner with friends in Pasadena at 7pm. She reads it again at home in Santa Monica at 1am. Over the weekend, she takes a trip to New York and reads it again. Twice. She decides not to answer the email, because her ex has stalked her in the past and she doesn’t want to communicate any further. But because of the tracking pixel, her email is always communicating, and it’s sharing info she does not want to send and doesn’t even know she is sending. She didn’t reply, but her ex still knows she read his email five times, including most likely in her bed. And he knows she took a trip to New York.
- A pedophile uses Superhuman to send your child an email. Subject: “Ten Tips to Get Great at Minecraft”. Your child keeps the email in their inbox and refers back to it often over the course of a year. Sometimes when they are at home in Vermont. Sometimes when they are at school in New Hampshire. Sometimes when they are with their grandparents in Massachusetts. Every time your child opens the email, that person knows generally where they are (or specifically, if they have other info to triangulate against).
- Superhuman decides they can make more money by supplementing their subscription fees with data licensing agreements. Maybe they decide to leave out data from paying Superhuman customers but they include location history from every single person you’ve ever emailed, because they have no contract with those people. Location maps with timestamps, other insights about things like working hours and locations, device types, and whatever else they collect. That data is then used to target those people in a variety of ways. If Superhuman is truly willing to commit to never license any data to anyone for any reason, they should be able to clearly say so right now. But they probably won’t, because they want to keep their options open.
I understand wanting to cover a new product, but an outfit as respected as the Times needs to go deeper on this stuff. Heck, I’m already at 4000 words — on a single subject — and I just wrote this on a whim over the weekend.
Even though I wish companies didn’t make the sorts of product decisions Superhuman has made, I’m glad they are at least showing their cards early (and appear to stand by them) so I can avoid their service. Not just on principle but because I have no reason to trust them with any of my data. Remember that they require full access to your Gmail in order to do their thing. Fast forward a year or two and I can see them licensing location data either from their own customers or their non-customers to a third-party for any number of distasteful purposes. They say they have a privacy policy that forbids this, but I don’t read their policy that way at all. It allows and even specifies all sorts of things they can do. Here’s an excerpt (emphasis mine):
HOW WE USE TRACKING TECHNOLOGY TO COLLECT INFORMATION
We automatically collect usage information when you visit our Website or use the Service through the use of tracking technologies, including tracking pixels and similar technology (collectively, “Tracking Technologies”). We may use the data collected through Tracking Technologies to: (a) remember information so that you will not have to re-enter it the next time you visit the Website or use the Service; (b) provide and monitor the effectiveness of our Service; (c) provide functionality of the Service including read receipts; (d) monitor and collect analytics data using third-party tools like Google Analytics in order to help measure traffic and usage trends for the Service; (e) diagnose or fix technology problems; and (f) otherwise to plan for and enhance our Service.
The form of this paragraph is very familiar to lawyers. Specify some stuff that sounds mundane and then leave yourself all sorts of escape routes. Item F is essentially a universal license to do whatever they want (i.e. “We’ve ‘enhanced’ our service by using your location data in a new way!”). Now, I’m not saying this privacy policy is out of the ordinary at all. I’m just saying there is nothing about Superhuman’s Terms of Service that prevent them from making further decisions that violate your privacy in the future. Not to mention, companies can change their policy at any time. When you use a product, you need to trust the people who are building it — not the documents their attorneys create. And finally, once again, because of this spyware pixel, most of the people they are collecting information on aren’t even Superhuman customers and never even signed up for this policy.
So what would I do if I were Rahul Vohra, Superhuman’s CEO?
The first thing I’d do is apologize and remove this functionality for everyone. You don’t need to take out a front page ad in the Times. Just own the mistake and disable the feature unless and until you can design it in an ethical way. Don’t keep it up for a year while you work on it. Take it down. This would show responsibility and regard for doing the right thing. A sign of an honorable company is when it is willing to learn, take responsibility, and improve.
Next I would recalibrate how important it is to even offer Read Receipts. Superhuman seems to be doing just fine in terms of customer satisfaction. I know some people like this functionality but does the success of Superhuman’s business depend on it? I would guess not.
Third, if Superhuman really cared about protecting the privacy of its users, they would actually provide the exact opposite of this feature. Protect all Superhuman users from emails loaded with surveillance pixels, do it by default, and never embed them in their own outbound emails. There are a few browser extensions that do this decently while keeping most benign images turned on, but this would be a great feature to have baked into an email client. Use this moment as a turning point to honor all of the other work going on at the company and turn this negative into a positive.
Finally, if I still didn’t agree that tracking the geolocations and reading behavior of unwitting people was deceptive, I’d wear it on my sleeve:
A good ethics test for investors, employees & users of Superhuman. If you use SH’s default spyware behavior, you should be willing to change your signature to this:
– Sent via Superhuman. Every time you open this email, the time and your location are sent to me.
Who’s first?
— Mike Davidson (@mikeindustries) June 27, 2019
A lot of Superhuman’s customers — and I assume most of its employees and execs — use the “Sent with Superhuman” signature already. If you are so sure that automatically receiving a recipient’s geolocation every time they read one of your emails is OK, you should be OK with telling them that when you send them an email. In fact, since it’s a feature you are proud of, you should be more than happy to market it so clearly, right? (In case you’re wondering, exactly zero people stepped up to do this. Not Rahul Vohra, no employees, no investors, and no customers.)
Before I close, I want to talk about blame.
I don’t automatically blame Superhuman designers for this, because I don’t know if they fought for it or against it. Likewise, I don’t blame Superhuman engineers, product managers, or anyone else, for the same reason. For all I know, this was something the team pushed back strenuously on and lost. If so, thanks for fighting the good fight, and you should have your equity grant doubled for trying to do the right thing. If not, this whole article also applies to you. The only person I know for sure shares some or all of the responsibility for this is Superhuman’s CEO, Rahul Vohra. He is the only employee I’ve seen actively defend it (although perhaps others have), and it’s safe to say he was intimately involved in its development.
This is also important: I do not know Rahul. I don’t know if he’s nice, mean, a good person, a bad person, likes his steak medium rare or well-done with ketchup, or anything else about him. I make no value judgements about him as a human, and as with most other humans, I try to assume the best about him. This article is about a very specific decision of his that I find to be dangerous and wrong. Whenever I see something like this, I always give the benefit of the doubt and assume the person simply doesn’t realize the downside consequences of their decision. I brought this up several months ago and the company did nothing to address it. I brought it up again last week and still nothing. In light of that, and in light of some of the responses from investors defending Superhuman’s surveillance behavior, I felt justified writing a proper piece about it.
Finally, if you are a user wanting to protect yourself against automatically having your email behavior and geolocation sent to people who use Superhuman and other surveillance tools, you need to do both of these things:
- Don’t use Superhuman yourself. As mentioned earlier, Superhuman leaves you unprotected from spying because they don’t allow you to block these spyware pixels. It also turns you into an unwitting information collection machine, aggregating info on every single person you send email to. Possibly including your parents, children, partners, and friends.
- Turn off remote image loading in whatever email client you use. Almost every client these days allows you to do this, with the strange exception of Gmail for iOS. If you are a Gmail user, I recommend switching to something like Outlook on your iPhone. It’s free and allows you to use your existing Gmail account. No migration necessary. Apple Mail is fine too.
So to sum up — whether you are an email provider or an email user — don’t surveil, and don’t allow yourself to be surveilled. I hope Superhuman does the right thing and decides to help stop this problem instead of trying to normalize it.


This is maybe the best, most-balanced, scrupulously fair, and therefore effectively damning indictment of a dark software pattern that I’ve ever read. Bravo.
My understanding is that Gmail clients proxy all images including the pixel tracking images, so this is a non-issue for gmail. Is that correct?
Any tips on how to uninstall and revoke it’s access?
That is an extremely handsome Maine Coon in the picture of this article.
The problem isn’t Superhuman, it’s all the other email clients that allow this tracking. I expect my email client to afford me privacy if I wish, at least as an option. That they don’t is the real problem.
HTML email has mostly been for ill. I take for granted that I carefully opt-in to loading images from some senders, but for most I don’t. This is me with 2 decades of email experience. We must inform the next generations of the nuances of what “load images” implies in email. Thanks for this terrific, critical article.
In my GMail -> Settings -> Images I have it set to always display images but my understanding was that recently Google started loading the images indirectly somehow and serving up a proxied copy to gmail users exactly to avoid this problem.
Google documentation on Gmail says:
Jack is partly right. Gmail does proxy images, so the sender shouldn’t be able to tell the receiver’s location, but they can still detect when (and how often) the email was opened if the receiver hasn’t turned off automatic remote image loading. See https://support.google.com/mail/answer/145919?p=display_images&rd=1
Thanks for the story my wife is a superhuman user
I don’t understand the image loading stuff. Can someone explain that a little more? Why should we be turning that off? Thanks!
Brian, whenever you load a web page your computer sends a request to the server providing the website, and so the server is able to log the time you requested the page, and roughly where in the world you are. But if you’re not logged in to the website they won’t necessarily know *who* you are.
If an email has images in it there are two ways those images can be provided – the image files could be included as part of the email message, or the images could be links to image files on a remote web server some time. It’s these remote images that we should be turning off. When you open an email that has remote images, if you want to see the images your email client will need to make a request to the web server that hosts those images. That server can then log that and deduce that you must have opened the email.
Hope that helps. You might also find https://en.wikipedia.org/wiki/Web_beacon useful.
Thank you very much for this piece.
I was not even aware that Superhuman existed, but now I know not only that I shouldn’t use it, but that I should advise others not to use it and decline to work with anyone by email who uses Superhuman, if I can possibly help it. I have also disabled all image loading in all email clients on all my devices.
I am sure they refuse to turn this functionality off because the ability to stalk recipients is a big part of what they are selling.
Superhuman, don’t be evil.
This is such an amasing post. I too wonder why people use Superhuman, but not for the issues outlined here. However, I’ve come to the conclusion that tracking of any kind is not good for the receiver.
I have to be honest here, I am using a tracker (within Gmail) but after reading this and wondering why I use it and why info is being recorded, for the tracking company, I think it’s not worth it due to the security issues you’ve outlined.
I’m so glad that this has come to light and thank you again for writing this piece and bringing it to my attention.
@Joe Crawford, @Barney Laurance:
The images are also moderately cached by Gmail, meaning that the logged timestamps will likely be nonsequential / skip repeated opens.
Five years ago I decided email was more trouble than it was worth because of crap includes like images. Worse I had complaints from companies I did not want emailing me because I would only accept 7bit ASCII and nothing else.
So I ditched email and guess what I don’t miss it in the slightest in my private life as I’ve told people if they want to speak to me then they can have the politness to pick up a phone and actually speak, otherwise it’s probably not important to them therefore it’s unlikely to be important to me.
And no I don’t do messaging apps either or gads forbid “social media” I’d rather grab a bottle of wine and go knock on their door.
The only thing that is true about social media is it’s a way your privacy is invaded as are very nearly all Internet communications systems…
Google and others grab bio-metrics where they can as well as invading your privacy. You know those hints and prompts as you type in the search box or other fields, that’s your typing cadence being captured in those companiess logs…
Very well written article, thank you!
When I did the onboarding onto Superhuman I mentioned similar concerns many times to the person who was doing the onboarding. I went so strongly as to say that this would be the one reason why I would choose to not use Superhuman.
I continue to give them this feedback, and no include your blog post link along with it.
I haven’t yet cancelled my Superhuman subscription, I am still hopeful that they will listen to feedback and good sense and remove the feature, but when it comes up for renewal in a few months this particular tracking behavior will likely make or break my continued relationship with them.
Excellent analysis. By default my mail clients don’t load images. Especially for commercial messages I generally don’t care enough about the contents to view it with “proper” formatting and tracking before deleting them. Wonder if there is/will be a Mozilla Thunderbird extension that simply rejects/deletes emails from Superhuman senders.
@Barney Laurance – Thank you for the explanation? Am I correct that the GMAIL app on iOS does not give you the option of turning remote image loading off?
Isn’t this blatantly illegal if the recipient is in the EU and protected by GDPR?
Thank you for this thoughtful, brilliant piece. It’s so on point — software that exploits the connections of its users is highly problematic. Another highly publicized, similar example was the ‘bug’ on Facebook that allowed Cambridge Analytica to scrape the profiles of a user’s friends when only the single user had consented. This sort of exploitation should be illegal — no company should allow a single user should to consent the collection of their connections private information.
A gmail plugin or browser extension that loads those tracking pixels, say, every hour for all time could be fun. And do it immediately on receipt a random large number of times, even for unread email.
Basically fight it by making it useless in a proactive manner.
@Brian – yes, that’s what the blog post above says. I don’t have any personal knowledge of that.
Just ordered the shower head. I get it the passion. Got to try this one. Great write up on the superhuman thing also.
This post is the just embarrassing. Any millennial who knows anything about tech and has had to look for a job in the past 3-4 years knows how to add one of the numerous extensions that already exist for individual users (not just mass mailing companies) to track when someone opens their emails. Regardless of the service the receiver is using.
This was the most pathetic sensationalist technology article I’ve read in the past year. I’m honestly embarrassed that you wrote this.
I have no stake in superhuman nor do I use it.
I hope the designers and engineers in the company did fight because this is bad design. It is like watching a worker punch a time card over and over – totally useless for anything but spying. And is the name of the company from Nietzsche?!? Run.
Section (f) is my favorite part from the privacy policy, too. Every single privacy policy has a version of it. It’s the part that says “we will do whatever we want with your data and you have no control and we won’t pay you even though our intent is to get rich off you.”
Is there no way to block emails sent from Superhuman, with an automated response saying something like “The intended recipient does not accept messages that provide data about the recipient to the sender”?
Gmail’s image proxy cuts both ways.
Because gmail caches the images, you can’t block *just* the SuperHuman tags. Even if you block them in-browser, they will still get a ping when Google caches them for you.
If I access my gmail account via the Mail app in iOS via IMAP does google still proxy? Separately, are the pixels from a specific domain that can be blacklisted using an ad blocker m, Etc? If so, what is that domain? Thanks.
Mike, thanks for taking the time to write this!
I agree that geo and repeated tracking is far too aggressive.
I don’t think we’ve arrived at this point with email tracking from numerous companies from a particularly nefarious, unethical or even amoral reasons. In the 90s email broke. Because of spam we ended up with an unreliable but critical communication channel and this “feature” is really a patch to an open loop.
It isn’t ideal but email not being delivered isn’t ideal either. I think we should now expect to have an email open event reported a single time.
Helluva piece, Mike.
thanks for the article.. it’s really worrying the ethical oversight that you see in so many companies entrusted with so much personal data.
it’s ridiculous that these never ending transgressions need to be identified and fought at the grassroots level, on a case by case basis..
For the record: I have never used Superhuman, nor do I know anyone from the company or anyone that invested in the company. Basically, I am completely unbiased.
There seems to be a lot of misunderstanding how gmail’s image caching works.
https://blogs.constantcontact.com/gmail-cached-images/
“We’ve tested our systems, and Constant Contact continues to accurately track your unique open rates exactly as it always has.
Where you may see a difference is within your “All Opens” reports. Since Gmail is caching the images on its own servers, a signal will only be sent to us at Constant Contact the first time the email is opened (or if the email is opened after Gmail has cleared its cache).
Essentially, this means that every individual instance of a subscriber with a Gmail address opening your email may not be reflected in your Constant Contact “All Opens” reports. Other email service providers are also reporting similar findings.”
Basically this means that Superhuman (and all bulk email providers) can track when the email was opened, but only the first time, and without identifying the location of the recipient (since the IP address of record is Google’s proxy)
And if gmail wanted to, they could cache the image as soon as it hit their server, further defeating any attempt to track the recipient.
While I agree that this does infringe on recipient’s privacy to a certain extent, it is far less nefarious as the article is making this out to be (since it’s only the first open and the recipient’s location is not disclosed.) As for non-gmail email, I feel that even if users aren’t technically savvy, software providers are, and they know that this is a problem for many years. Which is why most software providers disable remote images in HTML email. Perhaps it is the email providers responsibility to warn their users that if they enable remote images, the sender will be able to track them. Imagine if email providers said that they weren’t going to protect their users against spam? Why is failure to protect users against privacy any different?
In any case, while I do think there is a valid concern about email privacy, where is the outrage around other technologies that also infringe on privacy by default?
For example: WhatsApp
https://www.lifewire.com/whatsapp-read-receipts-ticks-3426871
Did you know that WhatsApp enables read receipts by default? Yes, it’s fairer than Superhuman, because unlike Superhuman, everyone has the same functionality. However, it’s still asymmetric because I would guess that most novice users do not know this function even exists, while all tech savvy users do.
In conclusion, while this article bring some good points about privacy, it was inaccurate about gmail (the leading email client), unfairly blamed Superhuman for common email practice, avoided placing any responsibility on the email providers, and didn’t mention other privacy infringing technologies like WhatsApp.
Can we find the domains used by SH? Creating an auto-delete filter for the entire domain, preferably one that also reports it as spam, seems appropriate. I like the idea of generating a large and random number of pings as soon as any message from a SH user arrives. Wonder if there’s a way to automatically forward it to Tor and have it bouncing all over the planet, opening several times a second for a few years?
Isn’t this in violation of EU GDPR law?
@Jack, you bring up some valid points, but WhatsApp’s read receipts are very different. They only let the sender know *whether* the receiver has read the message (before “now”), not when, how many times, or *where*. Moreover, as you alluded to, the receiver can reasonably know that this information about their behavior is being revealed to the sender, because they see it on their own screen as well. So WhatsApp’s read receipts are more like standard email clients’ read receipt practices, which this article *has* mentioned, aside from the fact that they are turned on by default. And since WhatsApp is a social messaging platform, rather than email, users’ expectations for the “liveness” of communication are different. Should concerns be raised about having social messaging read receipts on by default? Maybe so. But this article isn’t flawed by not mentioning every related and lesser privacy concern in communication apps.
This is absolutely a violation of GDPR. It doesn’t matter that they’re an American company, they’re producing software that collects, processes, and passes on without permission(!) PII about European citizens, so it’s covered under GDPR. It’s literally illegal in the EU.
@Lars: I’m a programmer and there is no technical reason why an email client has to access the remote image more than once. So if the email client was coded properly, only the first time that the recipient viewed the email (and agreed to download the remote images) would there be tracking. And for that I place the responsibility squarely on the software vendors lap. Pixel tracking (actually called web beacons) have been standard for years (probably over 10 years now.) Why isn’t is their responsibility to protect their users from all email vendors?
As far as WhatsApp is concerned, you give users way too much credit if they think they understand the technical difference between Facebook, WhatsApp, email, etc. A message is a message. And tracking is tracking. Another point, when WhatsApp was first introduced, it didn’t have tracking. It was added later. So the initial user base may very well be unaware that their messages are begin tracked.
@EU_resident: Pray tell how is an IP address considered PII???? That’s the only information being revealed here. (The sender already has the recipient’s email address so that can’t fall under PII)
Data subjects are identifiable if they can be directly or indirectly identified, especially by reference to an identifier such as a name, an identification number, location data, an online identifier or one of several special characteristics (e.g. physical, physiological, genetic, mental, commercial, cultural or social identity).
The GDPR states that IP addresses should be considered personal data as it enters the scope of ‘online identifiers’.
https://eugdprcompliant.com/personal-data/
https://www.whitecase.com/publications/alert/court-confirms-ip-addresses-are-personal-data-some-cases
Extremely fair assessment although I do disagree on the point that the team who implemented this is not at fault if they pushed back. I bet if one or two members of the early team had left over ethics, the feature wouldn’t exist and the culture would change. We live in the best job market ever; I’m not sure if just raising a concern to an exec is enough to absolve these employees of fault.
I instantly think of my experiences with QuickBooks invoice read receipts and my over the shoulder experiences seeing how CRMs like hubspot work. But this level is astounding.
Dr. Malcolm mentioned that we “could” but also asked if we “should” recreate dinosaurs. I’m ready to drop email altogether.
I have to agree with Thomas Jones. The article is embarrassing. None of this is new. Invisible pixels have been part of email since 1999 or so with the introduction of HTML emails. There is nothing unique to Super Human. Many many email clients have this feature. There are many GMAIL extensions that add the feature, that people use all the time. If you don’t want to be tracked, turn off automatic image load in your email client. Gmail introduced the ability to turn-off-images in the mid-2000s to give people the option to not be tracked. There is a lot of hate about SuperHuman here. It is misdirected. If anything, this article (and the comments) have taught me just how little people know about the basic fundamentals of email and how it works. Commentors should do some basic research before jumping in to ‘outrage-mode’.
I usually suggest several steps forward.
Use add blockers, they dont need your info. Im happy not looking at sites that require me to disable my blocker.
Find an encrypted email you like, use it. I use Tutanota but there are others.
Find an encrypted browser you like, use it. Ive used torr and epic. They are slower but how fast do you really need that web page to load.
Stop using google, your info is their business, consider alternatives like Duckduckgo.
Never give away anything you dont have to for convenience or that becomes the norm and you are then expected to give away more.
Some would ask what am I trying to hide. I respond I may like relations with my wife and dont do anything “evil” but that doesnt mean I leave the window wide open for anyone to see.
Agree with Patrick M. I LMFAO when reading this article. I’m a VP of sales and my sales teams have been using this feature for the last 10 years in various gmail extenions..
Still cant beleive that in 2019 people this is new technology and are butthurt!
Dont hate the player hate the game :) Another record quarter :)))))))
Great post. This was so on target — dead center bullseye. More business people should give thought to this — and then put a big poster up on the wall: Ethics starts here, right now, not tomorrow and not with someone else.
Too many see to buy into the business is all about the money. A better world getting built — even if the contribution is small? Seems not to matter to too many.
Thanks for advocating!
Question to the group here. Would the email headers have a reference indicating if an email was sent using SH or not?
@Jack
You argument seems to be the tracker should be useless (for the most part). If so then I think the post’s point about ethical behavior still applies. Here the group damaged would be those depending on the tracker’s value that pay for the mail services.
That then begs the whole question of why SH or any other company would see incurring costs for delivering the function are not reducing their profits — where is the incentive to include such functionality.
Finally, even giving the claim that existing service providers know and have taking the right actions to block (rather than partner and enable) and assuming that those looking to use the functionality and it’s working as advertised, you are basically saying it’s only the “weakest” in the world that are being preyed on. That seems a rather poor soapbox to be standing on.
@Scott
What company do you work for? I would like to know who not to do any business with.
If the players are willingly going the game it’s fine to have both the player and the game when the game is a morally or ethically questionable one.
You make some fair points on privacy in general in this article, however, to suggest that SH is purposely enabling creeps to creep on other people is far cry from what the services is truly all about.
Also, to put a negative spotlight on a small startup and use your popularity on twitter rally up the mob of trolls with partial information in order to force them to change their pixel tracking says more about your ego than your true desire to change privacy on the internet. Otherwise you’d be fighting your former employer(Twitter), FB and others who are equally as guilty and have made a far greater impact to our society (ad tracking, cookies, etc). But they are probably too big to go after.
As a former VP of Twitter design you should know that Twitter is not innocent from tracking people with pixels and other means.
Just some quick observations
– The title of this article is a bit link bait-is. “Top 5 ….” , “Spying”, etc.
– Creepy people will track you no matter the tool you are using. Just because creepy people use cars to follow other people it doesn’t mean cars are violating our privacy. Same goes for email, messaging apps, social network, etc.
– Tracking pixels are on pretty much every email client, app, website you visit on a daily basis. For example If you see an Ad, that’s a tracking beacon. Also, on this website you’ll find a email subscription form and that is pointing to a mail chimp website which means you are most likely using mail chimp, which also uses pixels to track email openings (and location) https://mailchimp.com/help/use-track-mailchimp/
– I do not track your email subscriptions, but I’m sure you have sent emails with pixel tracking in the past. We all have. To say we haven’t is hypocritical. (Even twitter, facebook, google, they all do)
– If someone cares about that level of privacy then there are apps that let you block all images, cookies from being loaded unless you approve each of them individually. In that case you will not see any tracking pixels (including SH).
– This article makes it seem like SH invented tracking pixels and they are maliciously trying to track you down or are building tools specifically to track others.
– If you have a website and you installed google analytics then you are doing the exact same thing. Specially if you apply it to registered users. (Have you been to a website looking at a certain product or service only to find it again on FB ? Those are tracking cookies)
– If you download chrome, open dev tools and click on network tab you can see all the calls that go out to ad providers when you visit random websites.
Based on these observations this article is a bit misleading and borderline trollish. If you are using some kind of analytics to track your views then you are also using tracking pixels.
For businesses, which is the true purpose for SH, the ability to know if a team mate or business partner received an email is actually very critical. Unfortunately there are far easier ways to track people that don’t require paying $30 a month …. survey services, FB, Twitter, phishing, etc etc… SH did not invent the pixel trackers. Advertising companies / ad engines did.
If you surf the net while sniffing your pockets (Chrome dev tools) you’ll see that the internet is plotted with tracking beacons. Why go after a services that’s truly aiming at making the painful process of clearing your inbox MUCH better?
Mike, we got distracted by the showerhead. My team really wants to know what the showerhead. The link goes to an Amazon page with a ton of showerheads. We are so curious, please help us.
Also thanks for the thoughtful insight on privacy.
John: Funny, Scott entered his email address into the form so I believe I know what company he works for and also what his actual title is. I won’t say anything more than that because I want to respect his privacy. Not sure he respects anyone else’s, but as I said in the original article, just because someone else is doing something bad, doesn’t mean you should.
Mike: Why so adversarial/hostile about Scott’s comment. He is correct, this is something that has been used for many many years. Saying that “You know the company he works for” sounds like a threat. Come on, let’s keep it pro. People are allowed to give their feedback, specially since you are the one who is shouting from the mountaintops. You have to expect some will disagree. Also, I saw that you saved their terms of services and waited for them to change it before you posted a copy of the previous one. Why not just send them a message and say “Hey guy, heads up, let’s edit this…”. instead you expected things to blow up and waited. If you truly care about privacy then why not just do something more constructive? I follow you and respect you. Let’s keep it pro.
If a Superhuman user with EU residence filed a simple complaint to the responsible data protection authority under GDPR (maybe with the help of http://www.noyb.eu), then it could get very interesting not only for Superhuman, but for a number of email clients and mail automation providers…
Steve: Sorry if I don’t take kindly to people calling other people who care about their privacy “butthurt” and trying to do some sort of victory lap about how much money invading people’s privacy has made them. Also, you are incorrect about the screenshot… it’s just an image version of the text I posted in my original article. I didn’t “wait” for anything. Posted it right upfront. Then someone notified me that Superhuman had just changed their page.
Rahul had a great, thoughtful response and fixed a lot of these things now. Will you write a follow up article saying he did that well?
@Scott I can only hope that your classic “Sales Bro!” response was written in satire.
I work in venture and am surrounded by Superhuman evangelists. I was an early-early adopter of tech like Tout App (remember them??) and Sidekick, which then became Hubspot Sales, and I view the sales use case as completely separate and irrelevant to the personal use case. After the novelty wore off, I stopped using email trackers firstly because they made me feel icky, and secondly because they were boring. Do you really need to know if someone has been opening your emails, and how many times? Only if you’re in sales (like our associates) or if you’re creepy. I now use a blocker, but unfortunately it doesn’t work for Gmail’s iPhone app.
Finally, a tip. Even if you don’t install Ugly Email or another blocker, one additional way to tell if you’re being tracked is to hover over the URLs within the email and look in the bottom left of your browser window. Tracking / masking *should* be revealed there.
I agree with ur view, and wish more people felt similarly about privacy more broadly with regard to mobile ecosystem / isps / web browsing / emails, ect. Just wanted to say for some of those responding in comments, that just cause ad tracking web beacons of any and all type in browser and emails have been around forever, does not mean that most of us are aware; or those who are may not be happy about it. It doesn’t make this activity legitimate just because it requires state/fed assistance in the form of privacy laws that neither party care to bother with. Now hafta deal with mobile and broadband isp’s doing the same thing full scale. Just because this bad behaviour more broadly has existed doesn’t mean it should not that we are not allowed past some point in time to have an issue with it still or ‘be late to being aware. I don’t like the level of permissions and control phone apps have. Just cause things are or have been or a certain amount of time has passed doesn’t make things honorable or right.
Mike: Ok I see your point. The tracking is a bit excessive. I want you to know that I’m still a big fan of you and little will change that. I just would have handled this a little differently. I looked at the Rahul’s twitter and he seems like a reasonable guy, so instead of blasting this out and calling him a spy / Darth Vader :) I would have tried to connect with him and see if there was a more productive approach to all of this. They seems like early stage and very receptive to feedback. I’m sure you did not post this to get more followers because you already have a lot, so @John above seems to be completely off and a bit rude (I would delete his comment, maybe). Also I think educating the reader on the broader use of pixel trackers (including on your website and pretty much everywhere else) would have seemed less vindictive (Not that it was). Anyway, just my 2 cents. Still a fan man. If there is a way to get an invite I could probably give a review as well. I’ve been waiting for a while.
Your post – interesting, thoughtful. I’m not sure I would call SuperHuman spies as the practice of read receipts (which I don’t like) have been around for sometime.
In the days since Rahul changed the direction completely – see: https://blog.superhuman.com/read-statuses-bdf0cc34b6a5 at the end of the blog post he even shares his email address inviting you to start a conversation.
Thanks for your raising the issue and its great to see a result like this.
I’m just getting caught up here. I’m not technical, but at first glance I thought the situation was much worst. I’m in marketing so without pixel tracking I don’t think we could track anything at all, specially on web based services. The location stuff was kinda creepy, but are they spying on people ? No, that’s over the top. Is google analytics spying on people ? No they use pixels and cookies to track views and sessions. Superhuman uses pixels to track when users open their email. Just like hundreds of services out there. Again, location stuff needs to be removed, I hope they at least do that.
As someone who spends most of their time being confused and disheartened as to why (that’s a philosophical why) greasy sales tactics manage to stink up a fair number of user experiences, this was a reassuring read.
Thanks Mike.
It is difficult to get a man to understand something when his salary depends upon his not understanding it.
This is an interesting article, I assume that as a professional journalist you would have validated your many assumptions with the company – can you confirm that?
Regards
Greg
Steve: Greg, why the need to validate assumptions? I believe it was clear in the original write up that the assumptions were just assumptions. Hence why I believed the headline was over the top given that it was based on assumptions. But that is up to Mike to choose based on who he wants to read this.
Here’s a thought experiment: Would people disagreeing with this post be happy sending the author a list of times and locations where they opened this post?
By the way even Google Analytics doesn’t let you filter this kind of information down to the individual visitor.
And yet, a HUGE portion of our GDP is now basically this. Facebook, Google, Amazon, all the telecoms and the ISP’s: everyone is collecting everything they can, and selling access to slices of it to anyone with a checkbook. (And that’s not to mention the three-letter agencies!) The revealed creepiness, in this particular case, is that END USERS can access this kind of tracking. You should point out that employees at all of these other companies, including hundreds and hundreds of 3rd-party “ad-tech” parasites, also have access to this sort of data as well, and let everyone be appropriately grossed out.
Dear Mike, It is but surprising as well as worrying to read about the spying techniques superhuman uses to spy on us using our emails. Your vivid article on the same has helped in bringing to light the methodologies used to derive details in the name of “Read Receipt”. As a journalist, it is an eye-opener for many using email as their main source of communication even till today.
Great post.
(Honestly, I think two out of the three use-cases for why tracking is bad are weak — Pedo/Terrorist/Criminal arguments are too often used to decrease privacy, and thus have some structural issues. The “do you trust this company to not betray you in the future?” is a much stronger argument, because we all get betrayed by commercial entities all the time.)
I think it is very interesting that the (few) comments that defend SH all embody, to use Mike’s phrase, the “lets exploit everything in the world that can act to our benefit” ethos.
And I think it’s something of a cultural divide. There are those who see people as resources to be exploited, and there are those who see people as persons, worthy of respect and dignity.
As far as I can tell the forces of greed and exploitation are winning, and perhaps will ultimately win. That’s why I applaud this article. You fight the good fight, even if — perhaps especially if — you can’t win.
Everybody knows about viruses and malware. Therefore it’s no longer the fault of virus or malware maufacturers or distributors, nor should they be called out or villified for this behaviour. “Others do it, so what’s the big deal.”
It is instead 100% each individuals fault for not protecting themselves. Victim blaming is the norm.
Such attacks on this article or defenses on Superhuman are just as disappointing as the above points.
I have had automatic loading of images turned off for years now, but have to turn many on as they are emails that I need to see, but much of the information (often what they are about) is hidden in images. As for Superhuman, how about extensions for other browsers that simply note which emails have been sent by it and repeatedly open and close the email in the background, flooding senders with receipts? Maybe they’d get the message.
Mike, thank you for writing this. Great stuff! I got here from Mike Monteiro’s article over on Modus/Medium ‘It Might Be Time to Start Flipping Tables’
From your screengrabs with the shrugger-investors to the phrase ‘tongue-bath’ (which I might need to co-opt) to your excellently illustrated bad things people could do with this technology…it’s stuff like this that just makes me want to take a time machine back to when my biggest privacy concerns were if my downstairs neighbor could hear me playing my records too loudly or if my parents ever found my old weird art journals. Next stop…Overton windoww wide ajar.
Mik,
As the long-time Executive Director of the Coalition Against Unsolicited Commercial Email, and a fellow privacy advocate, I SALUTE YOU. So very well constructed and said. Respect.
You mentioned that Superhuman requires access to all email. Does that mean Superhuman personnel can read the content of the email, or just the code/grpahics needed to track send and receive activity?
Thanks
*graphics
The article states that “geolocation” information is gathered from the recipient
This is FALSE
The location is that of the Internet Provider, NOT to the user
Not sure how an Ex or a Stalker could find that useful
Could somebody maybe send an example tracked mail to contact@wallflux.com?
I can then adjust the Wallflux Clearinghouse Google app script to catch superhuman-tracked email to remove the tracking pixel.
Thanks!
I find it interesting that John use the analogy “Creepy people will track you no matter the tool you are using. Just because creepy people use cars to follow other people it doesn’t mean cars are violating our privacy. Same goes for email, messaging apps, social network, etc.”
No matter what the medium, cars, cookies, tracking pixels, facebook data heuristics, or guns there will always be those that figure out how to exploit what was intended to be a positive feature in our lives. Most of us trade convenience for privacy every day without expecting that convenience to be exploited by person or entity with nefarious intent.
Many commenters were quick to come to the defense of the practice. As a point of reference of where our country has going, a crazy person who picks up a gun and kills someone… they family of the person killed can now sue the manufacturer. We never seem to blame the crazy person or perhaps it is purely an economic question of who has the most money. I use that as an example since you use cars. Consider if a drunk person gets behind the wheel of a car and kills someone. Can the family of the person killed sue the car manufacturer? I say, not yet.
Using the example Mike used in his article about the child predator, or stalker… if they succeed based on the use of the technology can the family sue the technology company that developed the tool used? Again, not yet. Think back when the metadata from photos taken by mobile phone cameras and then posted to facebook was decoded by child predators to find out, within minutes, a child was playing. An unattended child was snatched but later the predator was caught before he could harm the child. Again, a seemingly beneficial feature being exploited by the “creepy people”.
My point is that ethical behavior is part of the development of any feature, HW or SW. Something starts out with the best of intentions and then is exploited. It then becomes the responsibility of the feature creator or remove it, eliminate the exploit, or at least mitigate it. Many of the commenters say “it has always been like that” or “the number of exploits is so low given the number of positive transactions”. I don’t disagree. However, when the ability to exploit the feature becomes all too common, something must be done. Hopefully it doesn’t take congress to make it happen as in situation with facebook algorithms. Whether congress or public pressure precipitates the change, it is an ethical responsibility to change.
Anyway, just wanted to give a different view to consider for the millennials and long term tech users that the pendulum tends to swing from one side of convenience to the other of blame. Both sides cut with razor precision.
Tony: Good examples, and I agree with all of your points. At the same time, however, the technology here was created *expressly* to give people the power to pry without their recipients knowing. It wasn’t a clean feature that was then exploited bad people. It was a dirty feature that, in fact, *turned* good people into privacy violators. That’s what makes this example so clear in my mind.
We are a few months into this now and Superhuman is still violating people’s privacy.
Excellent analysis. By default my mail clients don’t load images. Especially for commercial messages I generally don’t care enough about the contents to view it with “proper” formatting and tracking before deleting them. Wonder if there is/will be a Mozilla Thunderbird extension that simply rejects/deletes emails from Superhuman senders.